Privacy and security
Search questions, keywords, articles
DATA ENCRYPTION AND PROTECTION
What is data encryption and why is it important?
Data encryption is the process of converting information into a secure code to prevent unauthorized access. It is crucial for protecting sensitive data from hackers.
How does encryption protect my personal information?
Encryption ensures that only authorized parties with the decryption key can read the data, keeping personal information confidential.
Are all types of data encrypted in modern systems?
Many systems encrypt sensitive data like passwords and financial info, but the extent varies depending on the platform's security measures.
Can encrypted data be hacked?
While encryption significantly reduces risk, no system is completely hack-proof. Strong encryption algorithms make unauthorized access extremely difficult.
What is data encryption and why is it important?
Data encryption is the process of converting information into a secure code to prevent unauthorized access. It is crucial for protecting sensitive data from hackers.
How does encryption protect my personal information?
Encryption ensures that only authorized parties with the decryption key can read the data, keeping personal information confidential.
Are all types of data encrypted in modern systems?
Many systems encrypt sensitive data like passwords and financial info, but the extent varies depending on the platform's security measures.
Can encrypted data be hacked?
While encryption significantly reduces risk, no system is completely hack-proof. Strong encryption algorithms make unauthorized access extremely difficult.
USER AUTHENTICATION AND ACCESS CONTROL
What is user authentication?
It is the process of verifying a user's identity before granting access to a system or data.
What are common types of authentication methods?
Common methods include passwords, biometrics (fingerprints, face recognition), and two-factor authentication (2FA).
How does access control improve security?
Access control restricts data and system access to authorized users only, minimizing risks from internal and external threats.
What is multi-factor authentication (MFA)?
MFA requires users to provide two or more verification factors, increasing security beyond just a password.
What is user authentication?
It is the process of verifying a user's identity before granting access to a system or data.
What are common types of authentication methods?
Common methods include passwords, biometrics (fingerprints, face recognition), and two-factor authentication (2FA).
How does access control improve security?
Access control restricts data and system access to authorized users only, minimizing risks from internal and external threats.
What is multi-factor authentication (MFA)?
MFA requires users to provide two or more verification factors, increasing security beyond just a password.
PRIVACY POLICIES AND COMPLIANCE
What is a privacy policy?
A privacy policy explains how an organization collects, uses, and protects user data.
Why is compliance with data protection laws important?
Compliance ensures that organizations meet legal standards, protecting user rights and avoiding penalties.
What are some common data protection regulations?
Examples include GDPR (Europe), CCPA (California), and HIPAA (healthcare in the US).
How can users check if a company respects their privacy?
Users can review the company's privacy policy and check for certifications or compliance seals.
What is a privacy policy?
A privacy policy explains how an organization collects, uses, and protects user data.
Why is compliance with data protection laws important?
Compliance ensures that organizations meet legal standards, protecting user rights and avoiding penalties.
What are some common data protection regulations?
Examples include GDPR (Europe), CCPA (California), and HIPAA (healthcare in the US).
How can users check if a company respects their privacy?
Users can review the company's privacy policy and check for certifications or compliance seals.
THREAT DETECTION AND INCIDENT RESPONSE
What is threat detection in cybersecurity?
It involves identifying potential security threats like malware or unauthorized access attempts.
How do companies respond to security incidents?
They follow incident response plans that include identification, containment, eradication, recovery, and lessons learned.
What tools are used for threat detection?
Tools include intrusion detection systems (IDS), antivirus software, and security information and event management (SIEM) systems.
Why is rapid incident response critical?
Quickly addressing threats minimizes damage and reduces downtime or data loss.
What is threat detection in cybersecurity?
It involves identifying potential security threats like malware or unauthorized access attempts.
How do companies respond to security incidents?
They follow incident response plans that include identification, containment, eradication, recovery, and lessons learned.
What tools are used for threat detection?
Tools include intrusion detection systems (IDS), antivirus software, and security information and event management (SIEM) systems.
Why is rapid incident response critical?
Quickly addressing threats minimizes damage and reduces downtime or data loss.
Top Frequently Ask Question
Sign in now to get $50 worth of crypto
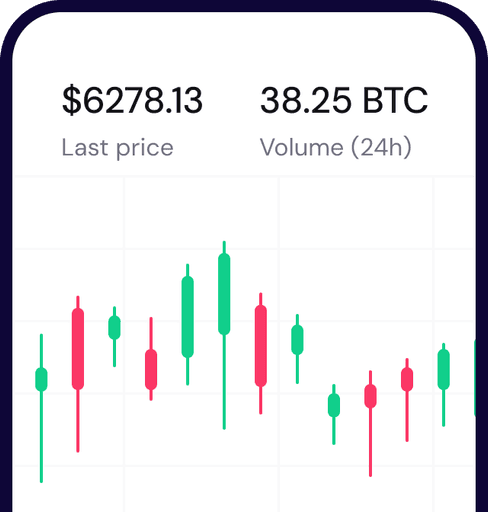
Scan to download Coinbank wallet